The progress made in cloud security is a key factor in keeping digital environments safe. As the year 2024 draws near, it’s becoming more and more important to guess where cloud security trends will go. Businesses’ digital footprints are always growing, and cyber threats are always changing. So protecting cloud platforms needs to be done proactively. This blog post offers insights about the current state of cloud security and also what the future holds for cloud security . To predict what will happen in the future, we need to closely identify the challenges of 2023. Our journey would not end with mere predictions, but it would extend to the evolution and progress of cloud security over time. The success or failure of the changing technologies depends on the historical trends and also on the changes in regulations..
On top of that, this blog goes beyond theoretical ideas by giving useful tips. Real-life case studies, best practices for implementation. Along with an overview of the challenges and possible roadblocks. We will also discuss the tools required to handle cloud security in 2024. Finally, we will also have a look at the cloud security consulting services. What type of cloud-based services are there, and which cloud experts provide the best cloud computing solutions. So, let’s start.
Unleash the power of the cloud with our expert guidance
Current State of Cloud Security
The cloud service providers of today do a lot to keep the info on their servers safe. This includes thorough background checks on employees to lower the risk of attacks from within and processes that keep data from one company from getting into the data of another. The user must still make sure that their passwords and connections are safe, just like they would if the data were kept locally. Let’s have a look at the current practices that are being followed.
-
Using encryption:
To keep data safe, data saved in the cloud is usually encrypted. This makes sure that even if someone gets access without permission, they can’t read the data without the right decoding keys. Many people use secure communication methods, like TLS/SSL, to encrypt data as it moves from the user’s device to the cloud server.
-
IAM (Identity and Access Management.)
To manage and control user access to cloud resources, strong IAM policies are in place. Multiple-factor authentication (MFA) and strict methods for verifying identity are part of this.
-
Checks and assessments of security:
Security reviews, audits, and compliance checks are done on a regular basis to find holes and make sure that rules and standards are being followed.
-
Plan for how to handle an incident:
Organizations and cloud service providers keep detailed incident reaction plans to deal with and lessen the effects of security incidents. This includes rules for finding security holes, fixing them, and moving on afterward.
-
Cloud-based security options:
A lot of people use security options that are made to work in cloud environments. This includes tools for keeping an eye on cloud systems, finding threats, and stopping intrusions.
-
Safety of Containers:
As containerization (like Docker) becomes more popular, it’s important to make sure that containerized apps are safe. This includes things like checking images, managing vulnerabilities, and protecting code during runtime.
-
Safety for APIs:
Because APIs (Application Programming Interfaces) are so important to cloud services, protecting these interfaces is a key part of protecting the cloud as a whole. This includes making sure that data sent through APIs is properly authenticated, authorized, and encrypted.
Evolution of Cloud Security
In the early days of cloud computing, there were many doubts surrounding the security that posed difficulty for many people to use it. At first, people weren’t sure about cloud technology because they were worried about things like data privacy, unauthorised access, and its overall reliabilityl. Over time, patterns in the past showed that cloud service companies worked together to solve these problems. This was a big turning point when models changed to where both users and companies are responsible for security. History shows that as technology got better, more and more attention was paid to encryption, identity management, and making security measures that work specifically in the cloud.
Effects of Technological Progress:
New technologies have played a major role in bringing transformation in cloud security practices. The use of both artificial intelligence (AI) and machine learning (ML) helped in identifying cyber threats. Now, automated tools are always looking for strange things and possible security holes. DevOps techniques have also become standard, which means that security is now built into both the development and operations processes. The development of safe coding methods and the general use of encryption technologies have been very important in making the cloud safer from new cyber threats.
The Part of Changes in Regulations:
The rules for Google cloud security have changed a lot because of changes in the laws. International organisations and governments agree on the need to set clear well defined rules to protect private data kept in the cloud. In Europe, the implementation of General Data Protection Regulation (GDPR) and other data protection rules around the world have made handling and storing of personal and sensitive data illegal. They have changed their security protocols to stay in line. This has made the cloud security setting stronger and more accountable.
Cloud Security Trends Predicted For 2024
-
Computing with Quantum Keys:
Quantum cryptography will become very popular in 2024. It will offer unbreakable security through quantum key distribution, which will be a big step forward in the fight against encryption breaches.
-
Threat detection based on AI:
Artificial intelligence will change from a tool to a guard for the internet. Machine learning algorithms will get better at finding complicated trends. This will make it easier to find and stop advanced threats in real-time.
-
Getting better at IoT security:
There are a lot of Internet of Things (IoT) gadgets, which is both helpful and dangerous. IoT security will make a big step forward in 2024 when standard protocols and built-in security measures will be the rule instead of the exception.
-
Mesh of cybersecurity
Businesses are using the idea of cybersecurity mesh to keep their data and investments safe in the cloud. With this method, you set up a distributed network and infrastructure that protects the people and devices that are linked to the network. Companies can directly control who can access their data and enforce security policies by using cybersecurity mesh, which is in line with the principles of Zero Trust architecture.
Infrastructure in the cloud is a big part of making AI available to everyone, which will bring about all the economic and social benefits that are promised. AI models, like the large language model (LLM) that runs ChatGPT, need a lot of computing power to be taught on a huge amount of data. Many companies don’t have the tools to do this on their own, but they can use this powerful and game-changing technology by using cloud platforms to access AI-as-a-service.
-
Hybrid and Multiple Clouds
By 2024, 85% of big businesses will have a multi-cloud strategy, which means they buy cloud services from more than one Cloud consulting companies. This is up from 76% in 2018. It saves money and gives you more options, but it makes managing data and connecting it to older systems more difficult. These new types of infrastructure (multi and hybrid cloud, which combine cloud with on-premises infrastructure) will continue to become more popular as businesses look for ways to balance security with freedom and pick and choose the services they need.
-
Real-Time Infrastructure for the Cloud
In 2024, businesses will maximise the use of real-time data to get the most up-to-date information instead of working on obsolete data. At the same time, we will be streaming more and more of the data we use. This includes movies and music from Netflix and Spotify, video data from Zoom or Teams calls, and new types of streaming leisure like cloud gaming. This means that cloud users will want more and more data storage options that allow for quick access, like Flash and solid-state drives.
-
Innovation and change driven by the cloud
As the AI described above, cloud computing can open the door to many other game-changing technologies, such as the Internet of Things (IoT), blockchain, and quantum computing. Because they don’t have to spend money on architecture and equipment directly, businesses can start “quick-win/fail-fast” projects to test the benefits of new technologies more easily than ever in 2024, thanks to cloud computing.
-
Safety and dependability in the cloud
Some of the most important features of cloud computer services that will become more popular as we move into 2024 are encryption, authentication, and disaster recovery. As hackers create new AI-powered attack methods, data steals and breaches are happening more often and getting worse. Also, any system that needs to be accessed by a person will always be vulnerable to social engineering attacks. This means that security and reliability are very important to both cloud service companies and their customers.
-
Cloud computing that lasts
All of the big cloud service companies have promised to be net-zero, both for their own businesses and to help the people who use their services cut down on their carbon footprints. Amazon has promised to have no pollution at all by 2040, and Microsoft wants to beat that goal by ten years. They have all said, like Google, that they want to get all of their energy from green sources. The push for cleaner and less harmful to the environment cloud computing will be a big trend in 2024. Whether they succeed is still unknown.
-
Being private in the cloud
Cloud privacy is the ongoing work on creating technical, legal, and regulatory tools. That will allow businesses to use the cloud while giving their customers peace of mind that all of their data is safe. Businesses usually give their data to a third party, usually the cloud computing services providers. Taking care of the privacy issues that come up because of this will remain a major theme in cloud computing in 2024.
-
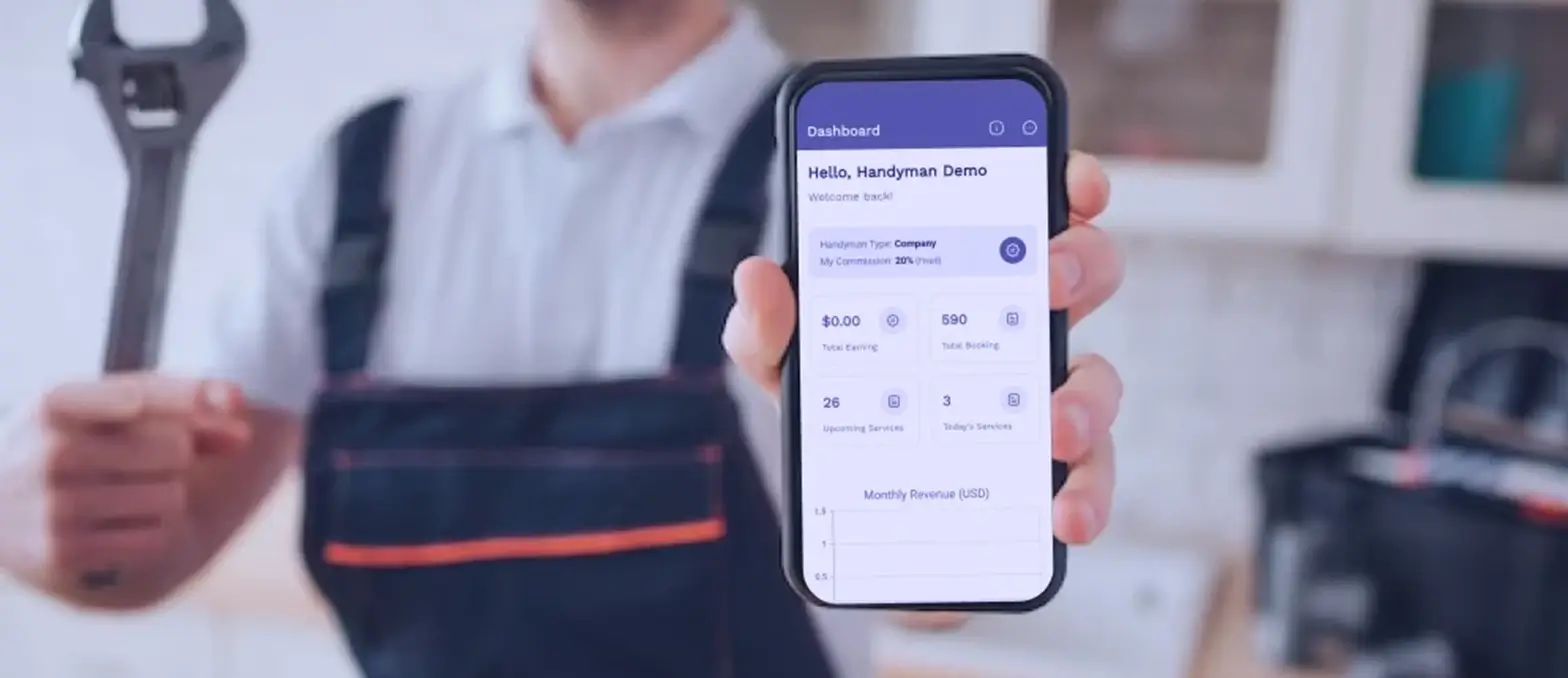
Cloud with no servers and pay-as-you-go
Serverless is a type of cloud computing service that lets businesses run their own servers without having to handle them. A normal cloud service might charge the company for the number of servers they want to host their infrastructure on. With a serverless model, the company only pays for the resources it uses. This saves money because the company doesn’t have to pay for computers when they’re not being used. It also gives the employees more time to work on their main tasks.
Technological Innovations Shaping Cloud Security
-
Rise of AI in Cloud Security:
The addition of AI to cloud security has been a huge step forward. By studying huge amounts of data in real time, AI is changing how threats are found and how they are dealt with. Patterns, outliers, and possible security holes are found by machine learning algorithms, which makes defenses faster and more aggressive. The growing use of AI in cloud platform security is a dynamic and flexible way to fight online threats that are always changing.
-
Blockchain and How It Can Help Keep Cloud Environments Safe:
Because it is autonomous and hard to change, blockchain technology is making waves in the field of cloud security. Blockchain improves data integrity in the cloud by making sure that information stays the same after it is saved. Smart contracts built on blockchain let people make deals that are safe and automatically carried out. This is a great step forward in cloud platform security because it not only makes data safer, but it also adds a level of trust and transparency to cloud activities.
-
What quantum computing means for cloud security:
When it comes to cloud computing trends, quantum computing brings both possibilities and challenges. Quantum computing could make it possible to break old encryption methods, but it could also create new encryption methods that can protect against quantum threats. Quantum-resistant cryptography and algorithms are becoming more and more important for getting cloud platform security ready for the age of quantum computing and keeping sensitive data safe.
Best Practices for Implementing Cloud Security Trends:
-
Assessing and Adapting to New Threat Vectors:
To stay ahead of the curve, you need to be proactive about finding and adapting to new threat vectors. It’s important to keep looking at possible risks and weak spots. This means doing regular security checks, penetration tests, and learning about new online threats. A strong cloud security plan changes security measures to deal with changing threat landscapes.
-
Why training employees is important:
When it comes to security, well-trained workers are the first line of defense because they care about people. It is very important to have training programs that teach employees about best practices for security, social engineering risks, and how important it is to protect data. An informed workforce is a big part of making an organization’s mindset security-aware.
-
Collaborative steps for safety:
Safety takes a group effort. As part of collaborative security measures, different offices, IT teams, and outside security partners should be able to talk to each other and work together. This way of working together makes sure that the defense plan is complete and well-coordinated. Sharing information about threats and the best ways to handle them makes a company safer overall.
-
Monitoring all the time and responding to incidents:
Continuous tracking is like having a security guard who is always on guard in the digital world. When cloud settings are monitored in real time, any suspicious activity can be found right away. When companies have a strong incident response plan, they can deal with security incidents quickly and effectively. Not only recognizing threats, but also having a clear plan for how to react and get back on track is very important.
-
Sorting data into groups and managing its lifecycle:
Every piece of data has a value, and knowing that value is key to good protection. Using data classification means putting information into groups based on how sensitive or important it is. This, along with lifecycle management practices that say how data is made, processed, stored, and finally thrown away, makes sure that security measures are right for protecting data at all stages of its lifecycle.
-
Users should get regular security training:
It is very important to give end users the skills they need to spot and deal with security risks. Users learn about phishing scams, social engineering, and safe online habits through regular security awareness training. Users who know about security issues add another layer of protection, making it less likely that they will be hacked and promoting an attitude of security within the company. With these extra steps, you can be even more sure that your cloud security is complete. A strong defense against the changing types of cyber threats in the cloud is made up of ongoing tracking, data classification, and training for users to be aware of these threats.
Are you ready to soar in the Cloud?
Connect with the leading cloud consulting company
Real-Life Examples of Effective Cloud Security Strategies
Some of the real-life examples of organizations that have effectively implemented cloud security strategies:
1. Netflix
- Strategy: Netflix utilizes a multi-cloud strategy, distributing its operations across different cloud providers.
- Implementation: They employ a combination of encryption, continuous monitoring, and automated response mechanisms to safeguard user data and ensure uninterrupted service.
2. Capital One:
- Strategy: Capital One has embraced a cloud-first approach, emphasizing the use of cloud services for agility and innovation.
- Implementation: They employ robust access controls, encryption, and automated compliance checks to secure customer data. Additionally, they use machine learning for anomaly detection to identify and respond to potential security threats.
3. Salesforce:
- Strategy: Salesforce, a pioneer in cloud-based customer relationship management (CRM), focuses on building a secure and compliant platform.
- Implementation: They implement strict identity and access management (IAM), encryption for data at rest and in transit, and conduct regular security audits. Salesforce also provides customers with tools to customize security settings based on their specific needs.
4. Adobe:
- Strategy: Adobe has transitioned to a cloud-centric model, offering services like Creative Cloud and Document Cloud.
- Implementation: They prioritize data privacy and security, incorporating features like data encryption, secure access controls, and real-time threat monitoring. Adobe has also invested in educating its users on best security practices.
5. NASA Jet Propulsion Laboratory (JPL):
- Strategy: JPL, part of NASA, relies on the cloud for its data-intensive scientific missions and projects.
- Implementation: JPL implements stringent security protocols, including encryption, network segmentation, and continuous monitoring. They use cloud services for scalability while maintaining a focus on data integrity and protection.
6. Workday:
- Strategy: Workday, a provider of cloud-based enterprise solutions, emphasizes data security and compliance.
- Implementation: They employ encryption for sensitive data, strict access controls, and regularly undergo third-party security audits. Workday’s cloud architecture prioritizes resilience and redundancy for uninterrupted service.
Challenges and Potential Roadblocks
-
Compliance Concerns:
Meeting regulatory compliance standards, such as GDPR, HIPAA, or industry-specific regulations, can be complex and demanding. Failure to comply with regulations may result in legal consequences, financial penalties, and damage to the organization’s reputation.
-
Balancing Security with User Experience:
Implementing stringent security measures may sometimes conflict with providing a seamless and user-friendly experience. If security measures are perceived as cumbersome or obstructive, users may seek workarounds, unintentionally compromising the organization’s security posture.
-
Budgetary Constraints:
Allocating sufficient resources for robust cloud security measures may be limited by budget constraints. Insufficient investment in security may expose the organization to potential vulnerabilities and hinder the implementation of advanced security technologies.
-
Integration with Legacy Systems:
Integrating cloud services with existing legacy systems can be challenging due to compatibility issues. Incompatibility may result in data silos, increased complexity, and potential security gaps, reducing the overall effectiveness of security measures.
-
Data Migration Challenges:
Transferring large volumes of data to the cloud can be time-consuming and may pose risks to data integrity during the cloud migration process. A Cloud consulting company can struggle a lot duw to Inadequate planning and execution of data migration. This can also lead to data loss, downtime, and potential security vulnerabilities.
-
Lack of Skilled Personnel:
The demand for skilled cloud security provider often exceeds the available talent pool.
Roadblock. A shortage of skilled personnel can hinder the implementation of effective security strategies, leaving organizations vulnerable to evolving cyber threats.
-
Vendor Lock-In:
Relying heavily on a single cloud service provider may lead to vendor lock-in, limiting flexibility and making it challenging to switch providers. Vendor lock-in can impede an organization’s ability to adapt to changing business needs, technology advancements, or negotiate favorable terms.
-
Insufficient Visibility and Control:
Maintaining comprehensive visibility into cloud environments and maintaining control over data and access can be challenging. Lack of visibility and control may lead to unauthorized access, data breaches, and challenges in responding to security incidents.
The A3logics’ Edge: Why Choose Us for Cloud Security Consulting Services?
A3logics is one of the best cloud consulting companies in the market, let’s see how:
-
Expertise Across Borders:
A3Logics has a team of seasoned workers who know a lot about cloud security. From figuring out the risks to putting plans into action, our experts have a lot of experience from working in a wide range of industries.
-
Solutions that are made to fit every problem:
One size doesn’t fit all is one of our strengths. We are proud at A3Logics to offer custom cloud security solutions that are made to fit the needs and difficulties of your business. Our customized method makes sure that you are fully protected in a way that fits your needs.
-
Strategies that are based on innovation:
What Makes Us Strong: Our goal is to always be ahead of the curve. When we do cloud security consulting at A3Logics, we use cutting-edge tools and new strategies. Your digital assets will always be safe with us; we don’t just protect them.
-
A Holistic Approach to Security:
Security isn’t just a box to check; it’s a way of thinking. A3Logics takes a comprehensive approach to cloud security, focusing not only on the technical aspects but also on the cultural and operational aspects to build a strong security environment.
-
Excellence in Compliance:
We are very good at finding our way through the governmental maze. A3Logics makes sure that your cloud security is in line with compliance standards that are specific to your business. Our knowledge makes sure that your business stays in line with the rules while using cloud technology to its full potential.
-
Open and honest communication:
Good relationships are built on clear communication. At every stage of our cloud security consulting services. A3Logics communicates clearly and without jargon because we value openness. There are no secrets, only results.
-
Monitoring and changing all the time:
We change with the threats, and they do too. At A3Logics, we as cloud consultants take a proactive approach by constantly watching and changing. We keep an eye on things to make sure that your cloud security can handle new threats.
-
Working together as a partnership:
We’re not just advisors; we want you to succeed with you. A3Logics encourages a partnership where everyone works together to understand your goals and problems and come up with answers that will help you succeed.
Design innovative cloud strategies with A3logics
Conclusion
So to wrap up, we all know technology is always changing and cloud security is one of the most important ways to keep the digital border safe. As we think about what we know and what we think will happen in terms of cloud security in 2024, it becomes very clear that the road ahead is both active and transformative. Our research has been an interesting trip through the worlds of strategy, technology, and resilience. From the historical weave of how cloud security has changed over time to the cutting-edge innovations that will shape its future. Picking a partner for cloud platform security is a very important choice. A3logics stands out as a leader in trust, innovation, and experience. Giving them a special edge in the field of cloud security consulting services.
One thing is clear as we come to the end of this discussion: the future of cloud security is both a challenge and a chance. To do this, you need to be willing to keep changing, work together, and be dedicated to staying ahead of the curve. With all it has to offer, the cloud begs businesses to take the plunge with confidence, knowing that the right plans, innovations, and relationships will not only protect their digital assets but also take them to new heights of success.
FAQs
1. What exact changes do you think will happen in cloud security in 2024?
Some of the trends that are expected to happen in 2024 are the growing importance of AI, the effects of blockchain on protecting cloud settings, the effects of quantum computing, and the difficulties and new ideas that come with using multiple clouds. Together, these trends are changing the way cloud security works.
2. How do these expected trends deal with the security problems that are happening now in the cloud?
The trends that are forecast for 2024 will likely deal with problems like making sure that encryption is strong, improving the ability to find threats, and managing security in complex multi-cloud environments. With improvements in technology and tactics, these trends aim to offer better answers to today’s security issues.
3. What does artificial intelligence have to do with the cloud security trends that would happen in 2024?
Artificial intelligence will be very important in 2024 because it will make it easier to find threats, handle security events automatically, and protect against new cyber threats in a smarter way. Researchers think that adding AI to cloud security methods will make them much smarter.
4. How can businesses get ready for the problems that come with using multiple clouds, as forecast by the 2024 trends?
Businesses can get ready for the challenges of adopting multiple clouds by giving their employees thorough security training, making sure that their security policies are the same across all of their cloud platforms, and keeping up with the newest technologies for handling security in a multi-cloud setting. This proactive method will help businesses get through the complicated process of adopting multiple clouds.
5. What effects does the rise of quantum computing have on cloud security, and what steps are suggested to deal with this trend?
The rise of quantum computing makes it harder for old security methods to work. To stop this trend, businesses should look into and use cryptographic and methods that are not affected by quantum mechanics. This proactive step makes sure that cloud security stays strong and can adapt to any progress made in quantum computer technology.