The Internet of Things (IoT) pertains to the interconnection of tangible devices, means of transportation, equipment, and other objects containing sensors, software, and networking technologies to collect and exchange information. This data can be analyzed to gain insights into users’ and systems’ behaviors and patterns and enhance efficiency by automating processes. This growth has been made possible by cost-effective sensors, wireless networks, and cloud computing that support new IoT applications in healthcare, transportation, manufacturing, and smart homes.
IoT offers various benefits, such as improved efficiency, reduced expenses, and an enhanced user experience. For example, in healthcare, IoT tools can track patients’ health, gather and evaluate data, and alert health practitioners during emergencies. In transportation, IoT-equipped vehicles can interact with other cars, traffic lights, and road signs to optimize traffic flow and minimize congestion. However, the rapid increase in IoT also presents considerable security challenges as the interlinking of devices makes them vulnerable to cyber-attacks. As such, it is crucial to develop and implement security measures that safeguard IoT devices and the information they collect and transmit.
IoT security is critical because these devices collect and transmit sensitive information that can put the user’s privacy and safety at risk if compromised. As such, IoT app development company must consider security measures at every stage of the development process to protect users and ensure data confidentiality.
The article intends to inform developers, IoT app development companies, and other stakeholders about the importance of security measures at every stage of the IoT application development process. By highlighting the essential security measures required, the article aims to help developers and companies ensure the safety and confidentiality of user data and protect against cyber threats. Ultimately, this article intends to contribute to the development of more secure and reliable IoT applications, enabling a safer and more efficient IoT ecosystem. In this article, we will highlight ten critical considerations and techniques for building secure IoT applications. From secure communication protocols to device authentication and encryption, these measures will help IoT developers and app development companies safeguard user data and prevent cyber threats. By implementing these security measures, developers can ensure that their IoT applications are safe and reliable, enabling users to benefit from the advantages of IoT technology without compromising their privacy and security.
Authentication and Authorization
Authentication and authorization are essential components of building secure IoT applications. IoT app development services must ensure that IoT devices are only accessible by authorized users and that the data transmitted is secure and confidential. Strong authentication protocols should be used to prevent unauthorized access. Two-factor authentication, biometric authentication, or a mix of both methods can be used to do this. Using a password and a security token as two different ways to confirm identities is known as two-factor authentication. Biometric authentication verifies a user by using biological traits like a fingerprint or facial recognition.
Authorization, on the other hand, involves defining and enforcing the permissions and privileges of different users or devices. IoT development services must use proper authorization mechanisms to prevent unauthorized access and prevent cyber threats. To implement strong authentication and authorization in IoT applications, IoT app development company should consider the following techniques:
- Secure communication protocols: IoT development services should use secure communication protocols such as SSL/TLS to encrypt data transmitted between IoT devices and servers.
- Password policies: Strong password policies should be implemented, requiring users to choose complex passwords that are changed regularly.
- Role-based access control: According to their functions and responsibilities, this should be utilized to provide various people or devices with varied rights.
- Multi-Factor Authentication: Multi-Factor authentication should be used by IoT development services to add an additional layer of security. This includes using security tokens or biometric authentication.
In IoT systems, authorization is required at multiple levels, including device-to-device, device-to-server, and server-to-server communication. Access controls must be put in place to ensure that only authorized devices or users can access specific IoT devices or data and that any communications between them are secure and private. Implementing strong authorization protocols in IoT systems can help to prevent cyber attacks, data breaches, and other security threats. Role-based access control (RBAC), for example, is a popular authorization technique used in IoT systems. With RBAC, users are assigned specific roles and permissions and are only allowed to access resources that are relevant to their role. This minimizes the risk of unauthorized access and data breaches and helps to maintain the integrity of the IoT network.
Encryption
Encryption is an essential security technique in the development of IoT applications. Data must be transformed into a secret code or cipher that can only be decoded by approved users or equipment. Encryption helps to protect sensitive data transmitted over the IoT network from unauthorized access and interception. In IoT systems, encryption is used to secure data transmissions between devices, servers, and other components of the network.
There are several encryption techniques used in IoT application development, including symmetric and asymmetric encryption. In contrast to symmetric encryption, which employs a single encryption key for both data encryption and decryption, asymmetric encryption utilizes two distinct keys: a public key for encryption and a secret key for decryption. In addition to encryption techniques, digital certificates are also used in IoT systems to establish trust between devices and servers. Digital certificates are used to authenticate devices and servers, ensuring that data transmissions are secure and private. The encryption techniques used must be strong enough to withstand attacks from hackers and other malicious actors. Encryption is an essential security measure in IoT application development services, helping to protect sensitive data transmissions from unauthorized access and interception.
Here are some best practices for encryption in IoT:
- Choose the right encryption algorithm: The encryption algorithm used in IoT applications should be strong enough to prevent attacks from hackers and other malicious actors. Popular encryption algorithms like AES and RSA are considered strong and are commonly used in IoT systems.
- Use keys appropriately: It’s important to keep encryption keys safe and avoid disclosing them to unauthorized parties. In addition, keys should be rotated periodically to prevent attacks on compromised keys.
- Secure storage and transmission of keys: Keys should be stored in a secure location and transmitted using secure protocols. This helps to ensure that the keys are not intercepted by hackers or other malicious actors.
- Use digital certificates: Digital certificates are used to authenticate devices and servers in IoT networks, helping to ensure that data transmissions are secure and private.
- Implement end-to-end encryption: End-to-end encryption ensures that data is encrypted throughout the entire data transmission process, from the source device to the destination device. This lessens the chance of data interception or unauthorized access.
Secure Boot and Firmware Updates
Secure boot refers to the process of validating the firmware of a device before it is allowed to boot up, while firmware updates refer to the process of updating the software that runs on the device. Both of these processes are critical for maintaining the security of an IoT system. Devices in IoT systems may be in remote or difficult-to-reach locations and frequently have limited resources. This makes it difficult to perform firmware updates, leaving devices vulnerable to security threats. To address this, mobile application development company and IoT developers can implement secure boot and firmware updates.
The secure boot assists in preventing the installation of unauthorized firmware on a device. It does this by verifying that the firmware has not been tampered with before allowing the device to boot up. This ensures that the device is running authentic and trusted firmware, reducing the risk of unauthorized access or malicious attacks. Firmware updates, on the other hand, are critical for addressing security vulnerabilities that may be discovered after a device has been deployed.
To implement secure boot and firmware updates, developers can use secure boot loaders and implement secure update mechanisms. Secure boot loaders are responsible for verifying the integrity of the firmware before allowing it to boot up, while secure update mechanisms ensure that firmware updates are secure and can only be applied to devices that are authenticated and authorized.
Best Practices for Secure Boot in IoT:
- Implement a secure boot loader: A secure boot loader can help to ensure that only trusted firmware is loaded and executed on the device. The boot loader should verify the authenticity of the firmware before it is loaded.
- Use secure storage: The keys and other security parameters used in the secure boot process should be stored in a secure and tamper-resistant storage device.
- Protect the bootloader: The bootloader should be protected from unauthorized access and tampering. Access to the bootloader should be restricted to authorized personnel only.
- Implement hardware root of trust: A hardware root of trust can be used to establish a chain of trust that extends from the hardware to the firmware, ensuring that only trusted firmware is loaded and executed on the device.
Best Practices for Firmware Updates in IoT:
- Use secure update mechanisms: Firmware updates should be delivered using a secure update mechanism that ensures that only authorized and authenticated firmware is installed on the device.
- Authenticate the firmware: The firmware should be authenticated before it is installed on the device. Digital signatures or other forms of authentication can be used for this.
- Use encryption: Encryption should be used for firmware upgrades to prevent tampering and unwanted access.
- Test firmware updates: Firmware updates should be tested thoroughly before they are deployed to ensure that they do not introduce any new vulnerabilities or cause any problems.
Network Segmentation
Network segmentation is a security technique used to divide a network into smaller, more secure subnetworks. In the context of the development of IoT applications, network segmentation can help to mitigate security risks associated with the deployment of large numbers of devices that are connected to a common network. By segmenting a network, IoT developers can isolate devices and limit the potential impact of a security breach. For example, if an attacker gains access to one device on a network, network segmentation can prevent them from accessing other devices on the same network. Some best practices for network segmentation in IoT include:
- Limit the number of devices on each segment: To minimize the potential impact of a security breach, IoT developers should limit the number of devices that are connected to each segment of the network.
- Use virtual LANs (VLANs): VLANs can be used to create logical segments on a single physical network, enabling devices to be grouped together based on their security requirements.
- Implement access controls: Access controls, such as firewalls and authentication mechanisms, should be used to control access to each segment of the network.
- Monitor network traffic: Network traffic should be monitored to detect any unusual activity which may indicate a security breach.
- Keep software and firmware up to date: Regularly updating software and firmware on IoT devices can help to address any security vulnerabilities that may be discovered.
Access Control
Access control is a crucial aspect of security in IoT, and it involves controlling and managing access to devices and data within a network. The top mobile application developer in USA recommends implementing access control measures to prevent unauthorized access to IoT devices and data. Some best practices for access control in IoT include:
- Implementing user authentication: User authentication is an essential part of access control and involves verifying the identity of a user before granting access to IoT devices and data.
- Implementing role-based access control: According to their roles and responsibilities, users are given access levels that vary under role-based access control. For instance, an administrator may have full access to all devices and data, while a regular user may only have access to certain devices and data.
- Implementing device authentication: Device authentication is another essential aspect of access control, and it involves verifying the identity of a device before allowing it to access the network.
- Implementing access control lists (ACLs): Access control lists are used to define which users and devices have access to specific resources on the network.
- Regularly reviewing access control policies: Access control policies should be regularly reviewed and updated to ensure that they are effective and up to date.
Vulnerability Management
Vulnerability management is an essential aspect of security in IoT, and it involves identifying, assessing, and mitigating vulnerabilities in IoT devices and networks. Vulnerabilities can arise due to various factors, including outdated software, weak passwords, and unsecured communication channels, among others. IoT developers should implement robust vulnerability management processes to ensure that their devices and networks remain secure over time. Some best practices for vulnerability management in IoT include:
- Conducting regular vulnerability assessments: Vulnerability assessments involve identifying vulnerabilities in IoT devices and networks, and IoT developers should conduct them regularly to identify and address new vulnerabilities as they arise.
- Prioritizing vulnerabilities based on severity: Not all vulnerabilities are created equal, and IoT developers should prioritize vulnerabilities based on their severity and potential impact on the device or network.
- Developing and implementing a vulnerability management plan: A vulnerability management plan should outline the steps that IoT developers will take to identify, assess, and mitigate vulnerabilities in their devices and networks.
- Regularly updating and patching software: IoT developers should ensure that their devices and networks are running on the latest software versions and should regularly update and patch software to address known vulnerabilities.
Monitoring and Logging
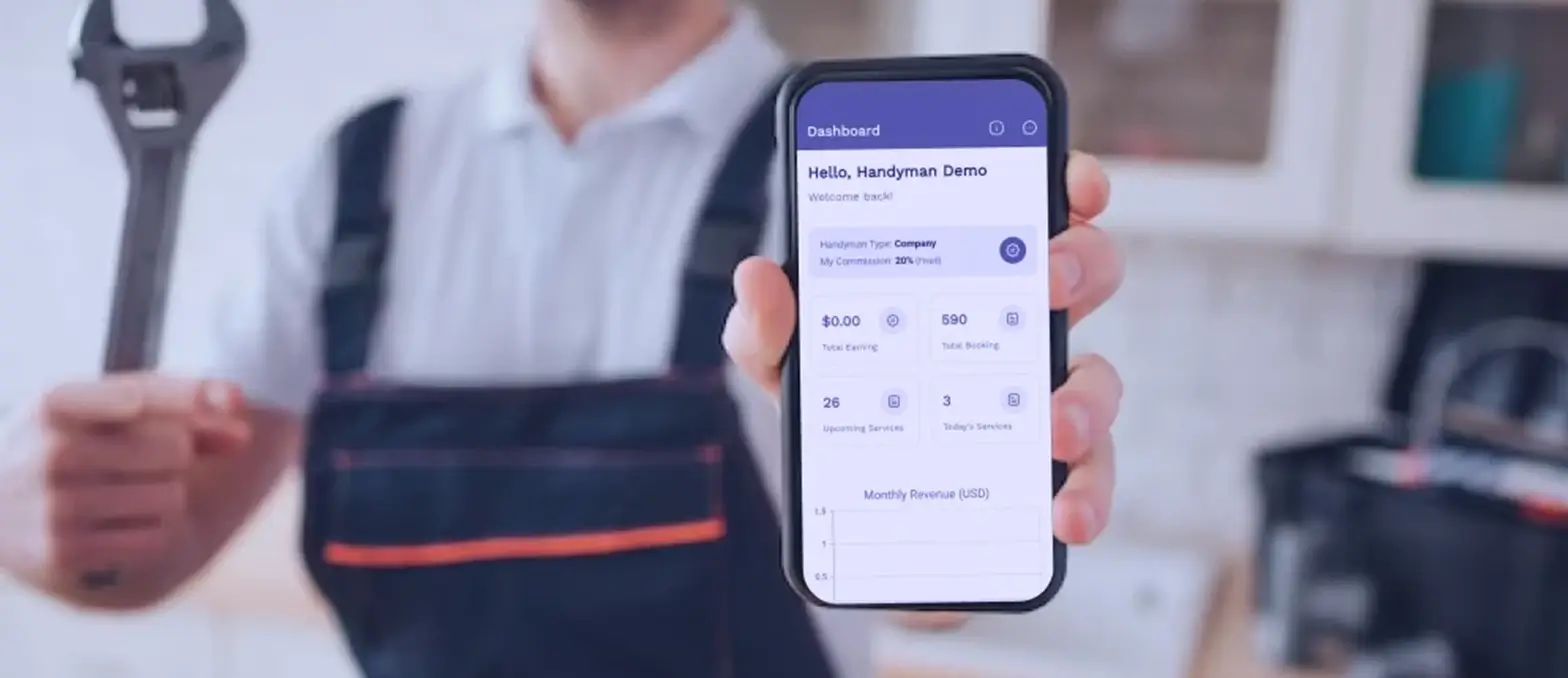
Monitoring and logging are essential components of IoT security, as they enable IoT developers to monitor their devices and networks for anomalies and suspicious activity, as well as to track the activity and behavior of users and devices over time. In iPhone app development and other IoT applications, monitoring and logging can be used to detect unauthorized access attempts, identify potential security threats, and monitor the behavior of IoT devices and networks. Monitoring and logging can also be used to identify potential performance issues, such as devices that are consuming excessive resources or networks that are experiencing bottlenecks. To implement effective monitoring and logging in IoT, developers should consider the following best practices:
- Implement centralized logging: Centralized logging enables developers to consolidate log data from multiple sources and analyze it in real time, providing a comprehensive view of the security and performance of IoT devices and networks.
- Monitor network traffic: By monitoring network traffic, developers can identify potential security threats, such as unauthorized access attempts or unusual data transfers.
- Implement user activity logging: User activity logging can help to track the behavior of users and identify potential security threats, such as unusual login attempts or unauthorized changes to device settings.
- Implement real-time alerts: Real-time alerts can be used to notify developers of potential security threats or performance issues, enabling them to take immediate action to mitigate risks.
- Use machine learning and AI: Machine learning and AI can be used to analyze log data and identify potential security threats or performance issues, providing developers with valuable insights into the behavior and activity of IoT devices and networks.
Physical Security
Physical security is an important consideration in IoT, as it involves the protection of physical devices, systems, and infrastructure from unauthorized access or damage. In IoT, physical security can include measures such as securing physical access to devices, restricting access to sensitive areas, and implementing surveillance and alarm systems. In IoT, physical security is particularly important because IoT devices are often distributed across different locations, making them vulnerable to theft, damage, or tampering. For example, a connected device in a public area, such as a smart parking meter or a smart traffic signal, could be physically damaged or tampered with, compromising its security and functionality. To ensure the physical security of IoT devices, developers and system administrators should consider the following best practices:
- Secure physical access to devices: IoT devices should be installed in secure locations with restricted physical access to prevent unauthorized tampering or theft.
- Implement surveillance and alarm systems: Surveillance and alarm systems can be used to monitor IoT devices and alert security personnel in case of suspicious activity or unauthorized access attempts.
- Use tamper-evident seals: Tamper-evident seals can be used to detect physical tampering with devices or equipment, making it easier to detect and address potential security threats.
- Implement regular maintenance and inspections: Regular maintenance and inspections can help to identify potential physical security risks, such as devices that are in need of repair or replacement.
- Implement secure storage and transportation: IoT devices should be securely stored and transported to prevent theft or damage during transit.
Supply Chain Security
Supply chain security is an important aspect of IoT security, as it involves the protection of the entire supply chain, from component manufacturers to the end user. In the IoT of Android App Development Services, supply chain security can include measures such as ensuring the security of hardware and software components, verifying the authenticity of components and their sources, and monitoring the supply chain for potential security threats. To ensure the supply chain security of IoT devices, developers and manufacturers should consider the following best practices:
- Implement secure development practices: Secure development practices can help to prevent vulnerabilities from being introduced into devices during the development process.
- Verify the authenticity of components and sources: Components and their sources should be verified to ensure that they are genuine and not compromised.
- Monitor the supply chain for potential threats: The supply chain should be monitored for potential threats, such as counterfeit components, malware, or other security risks.
- Implement secure communications: Secure communications can be used to protect data transmitted between different components in the supply chain, helping to prevent data tampering or interception.
- Implement secure storage and transport: Components should be securely stored and transported to prevent tampering or theft during transit.
Software Update and Patch Management
Software updates and patch management are critical components of IoT security. The security of IoT devices can be compromised if they are not regularly updated with the latest security patches and software updates. This is because vulnerabilities in the software can be exploited by attackers to gain access to the device and its data. To ensure the security of IoT devices, developers and manufacturers should consider the following best practices for software updates and patch management:
- Regularly update devices: Regular software updates should be provided to ensure that devices are protected against the latest security threats and vulnerabilities.
- Use automated updates: Automated updates can be used to ensure that devices are updated quickly and efficiently without requiring user intervention.
- Implement a patch management process: A patch management process can be used to ensure that security patches are quickly identified and deployed to devices in a timely manner.
- Test updates before deployment: Updates should be thoroughly tested before deployment to ensure that they do not cause any unintended consequences or introduce new vulnerabilities.
- Provide clear instructions to users: Clear instructions should be provided to users on how to update their devices and the importance of regularly updating their devices.
IoT development services can ensure the security of their devices and protect against potential security threats. It is important to prioritize security updates and ensure that they are regularly deployed to devices to minimize the risk of security breaches. Failure to implement proper software updates and patch management can result in serious security vulnerabilities, leaving devices and their users at risk of attack.
Conclusion
Building secure IoT applications is essential to protect against potential security threats and ensure the safety of devices and their users. Implementing best practices such as authentication and authorization, encryption, secure boot, and firmware updates, network segmentation, access control, vulnerability management, monitoring and logging, physical security, supply chain security, and software updates and patch management can help improve the security of IoT devices. As IoT technology continues to grow and become more prevalent, it is crucial that companies prioritize security in their IoT app development services. By implementing these best practices, companies can protect their devices from cyber attacks, safeguard sensitive data, and build trust with their users.
A3logics urges companies that are developing IoT applications to take security seriously and implement these best practices to ensure that their devices are secure. Additionally, users should be aware of the potential security risks associated with IoT devices and take steps to protect their personal data. By working together, we can create a safer and more secure IoT environment for everyone.
FAQ’s
Q: What is IoT?
A: The “Internet of Things” (IoT) is a collection of physical devices, household appliances, and other objects that include connection, software, and sensors to allow for data gathering and sharing.
Q: Why is IoT security important?
A: IoT devices are vulnerable to cyber attacks, which can compromise personal data, affect system performance, and cause harm to users. Prioritizing security in IoT app development can help safeguard against these risks.
Q: What are some common security risks associated with IoT devices?
A: Common security risks associated with IoT devices include insecure network connections, vulnerabilities in device software, weak authentication, and access controls, and inadequate data encryption.
Q: Which best practices exist for creating secure Internet of Things applications?
A: Best practices for building secure IoT applications include prioritizing authentication and authorization, implementing encryption, securing boot and firmware updates, network segmentation, access control, vulnerability management, monitoring and logging, physical security, supply chain security, and software updates and patch management.
Q: How can companies prioritize security in their IoT app development services?
A: Companies can prioritize security in their IoT app development services by conducting regular security audits and risk assessments, implementing security protocols and best practices, and staying up-to-date on the latest security trends and technologies.
Q: How can IoT users protect their private information?
A: Users should prioritize data privacy by using strong passwords, keeping software up-to-date, being cautious of suspicious emails or requests, and reading privacy policies carefully before using new IoT devices or services.
Q: How has the growth of IoT impacted security risks?
A: The growth of IoT has increased the number of connected devices and expanded the attack surface for cyber threats, making security risks more complex and challenging to manage.